Safeguard Remote Access is designed for modern remote work and third-party support. Access is delivered through a browser-based experience and supports privileged connections over standard protocols like RDP and SSH, while keeping access controlled and auditable.
What you can achieve with Safeguard Remote Access
- Enable VPN-free remote access to privileged resources from anywhere
- Improve productivity with a browser-based approach and no client software to install
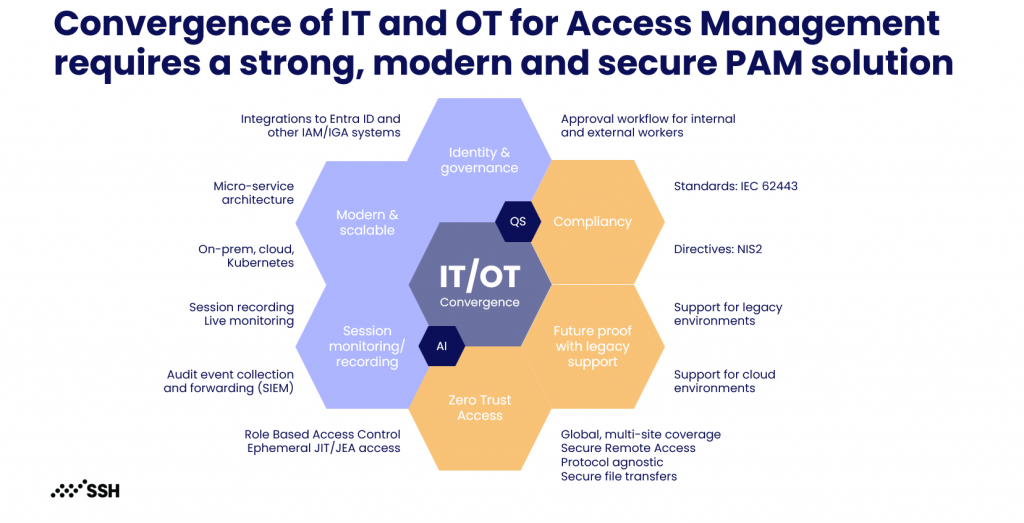
- Deliver Zero Trust Network Access (ZTNA) for privileged admin access
- Connect to critical systems using out-of-the-box support for RDP and SSH
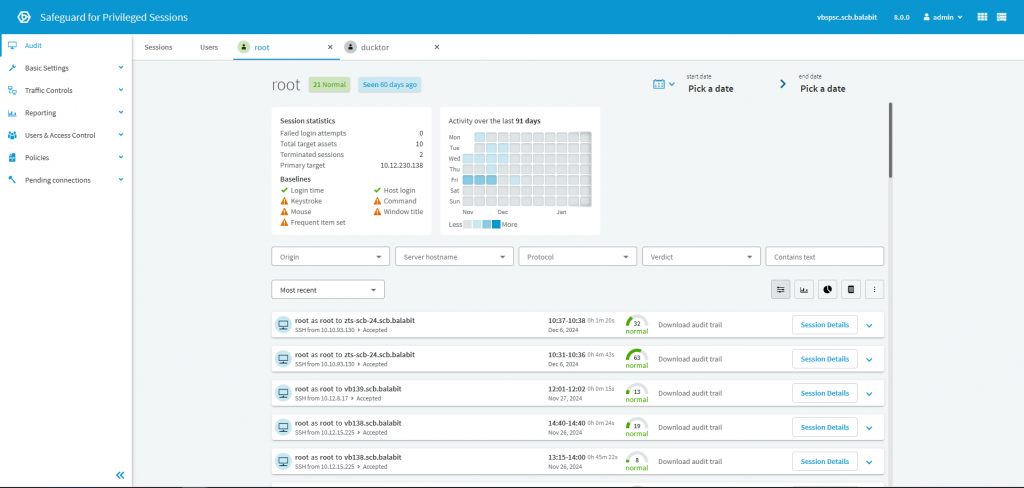
- Add session monitoring and recording by integrating with Safeguard for Privileged Sessions
How Security Accent delivers Safeguard Remote Access successfully
We implement Safeguard Remote Access as part of a practical privileged remote access capability, not only a connectivity feature. We help you define scope and target resources, design the access model and policies, integrate authentication and MFA where required, and onboard priority systems in phases to ensure secure adoption and strong auditability.
Our typical delivery includes
- Scope definition (privileged users and contractors, target systems, remote access scenarios)
- Target architecture and rollout plan (SaaS model, connectivity approach, phased onboarding)
- Identity integration and policy baseline (directory authentication, groups/roles, MFA and step-up where required)
- Resource onboarding and protocol enablement (RDP/SSH access setup, access boundaries)
- Session oversight and evidence where required (integration with Privileged Sessions, reporting, runbooks, knowledge transfer)
Need help with Safeguard Remote Access?
Share your remote access scope, priority systems, and vendor or contractor access needs. We will respond with recommended next steps. If you prefer to talk first, book a short discovery call.