Identity Governance & Administration
Identity Governance & Administration (IGA): what it is and what it delivers
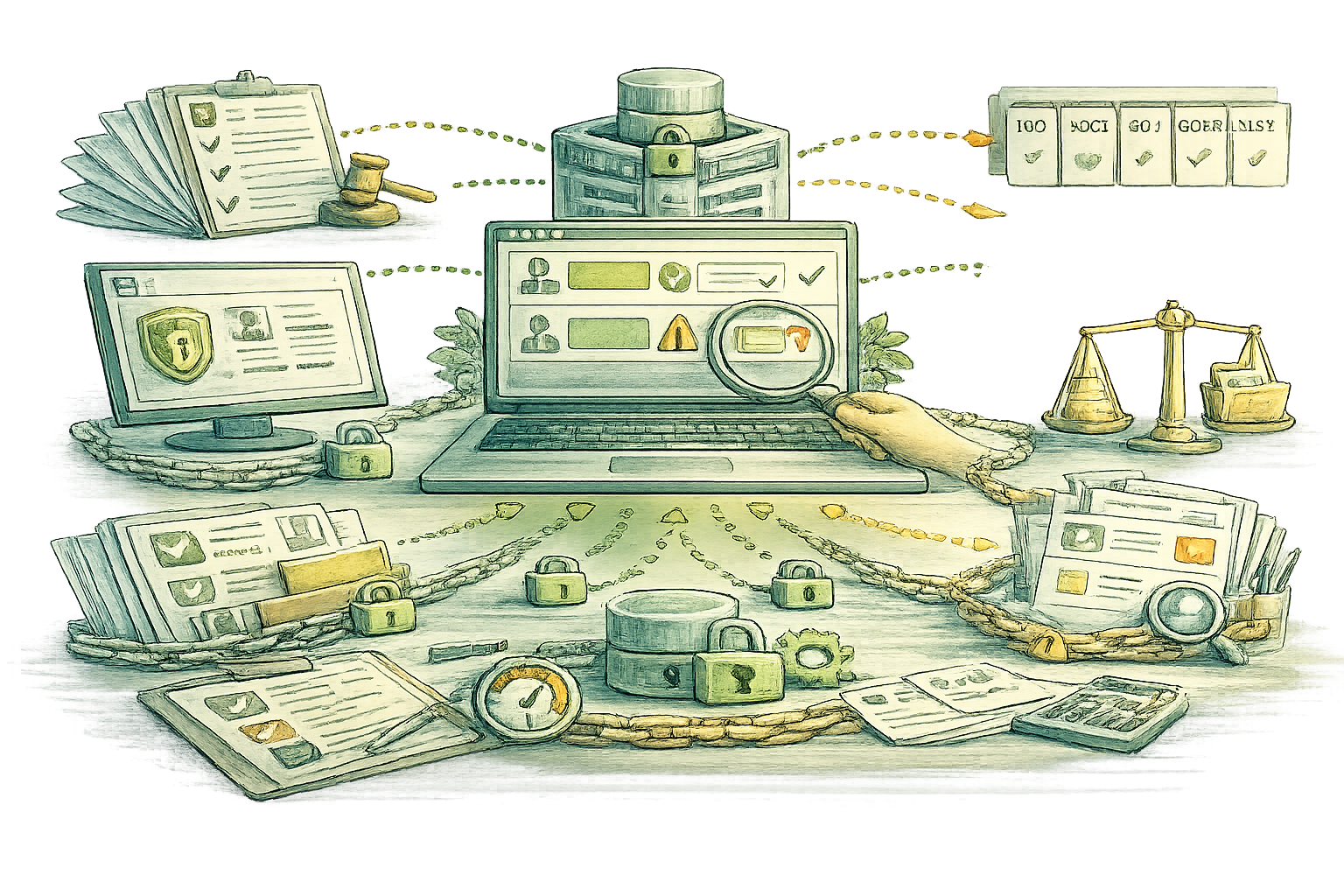
Identity Governance helps you control who has access to what across your applications, and ensures access is granted, reviewed, and removed in a consistent and auditable way.
IGA delivers value only when it is scoped correctly and rolled out in a structured manner. Many initiatives fail or remain limited in coverage because ownership, processes, and application onboarding are not defined upfront.
We help you do IGA the right way, with a practical roadmap, a phased rollout approach, and measurable outcomes across your critical applications.
Clarify your identity governance needs and requirements in a short call. We will align on your priorities, scope, and the next best step, assessment, workshop, or implementation.
Prefer to describe your scope first? Submit the following request and we will come back with next steps Send an IGA request to us.

Identity Governance & Administration
What IGA Delivers
- Identity Lifecycle Management (Joiner, Mover, Leaver)
- Access Request and Approval Workflows
- Automated Provisioning and Deprovisioning
- Role and Entitlement Governance (RBAC/ABAC Support)
- Access Certifications and Periodic Reviews
- Segregation of Duties (SoD) and Policy Controls
- Identity Data Quality and Authoritative Sources
- Audit, Compliance Reporting, and Evidence Management
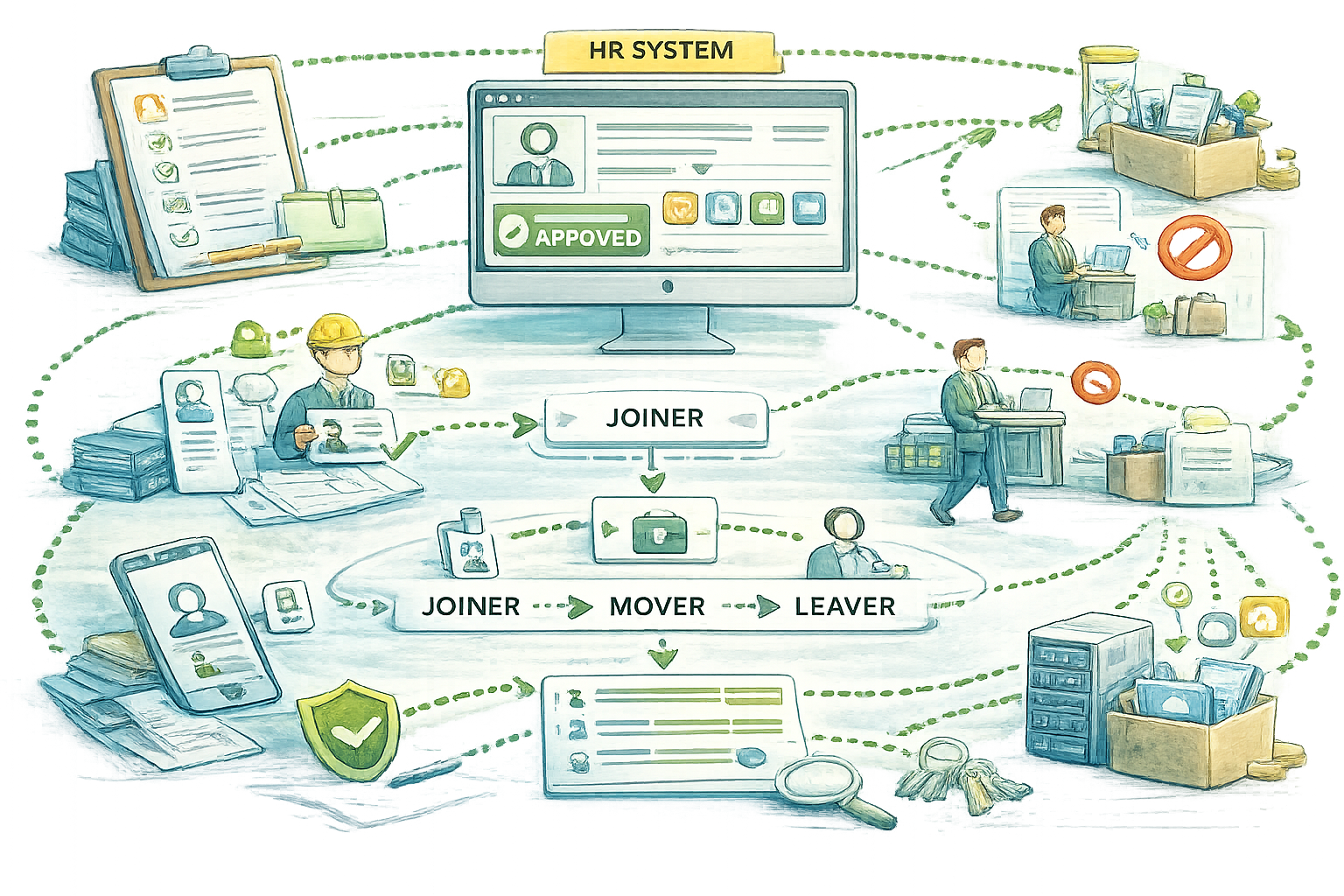
Identity Lifecycle Management is the engine that turns HR and business events into the right accounts and access, at the right time. When someone joins, changes role, or leaves, the capability orchestrates everything end to end: identity creation, account linking, entitlement changes, and clean offboarding across your applications and directories. It is also where you model ownership and accountability so every identity has a clear “source of truth” and a controlled lifecycle, not a collection of manual updates.
The result is faster onboarding and smoother internal moves, with far less manual admin effort and fewer errors. It reduces orphaned accounts and “access creep,” enforces least privilege by default, and gives you consistent traceability of who had what access and why. In large, heterogeneous environments, this is exactly how you scale application onboarding and governance without turning IAM into a ticket factory.
Access Request and Approval Workflows provide a structured, user-friendly way for people to request the access they need, while the organization keeps control. Instead of ad-hoc emails and unclear decisions, requests follow defined paths: the right approvers, the right checks (like role fit and policy constraints), and the right evidence captured automatically. This capability is where governance becomes practical, because it turns “process” into an auditable workflow that business and IT can both live with.
The benefit is a predictable, compliant access process that is faster for users and safer for the organization. You reduce approval bottlenecks with clear routing and delegation, improve decision quality by giving approvers the right context, and maintain a complete audit trail of request, approval, and fulfillment. Done well, it also cuts rework and exceptions, and supports scalable access governance across hundreds of applications.

Automated provisioning turns identity events into real access changes, without waiting for tickets. When a customer registers, upgrades, changes a subscription, or becomes inactive, the right accounts, groups, roles, and entitlements can be created, updated, or removed across your connected applications. The capability typically includes policy-based rules, connectors and APIs, and reconciliation to keep systems aligned even when changes happen outside the main platform.
Benefits: Faster time-to-access for new users and new services, fewer manual errors, and much lower risk of orphaned accounts or “forgotten” privileges. It also improves operational efficiency by reducing repetitive admin work, strengthens least-privilege by keeping access current, and makes audits easier because access changes are consistent and traceable end-to-end.

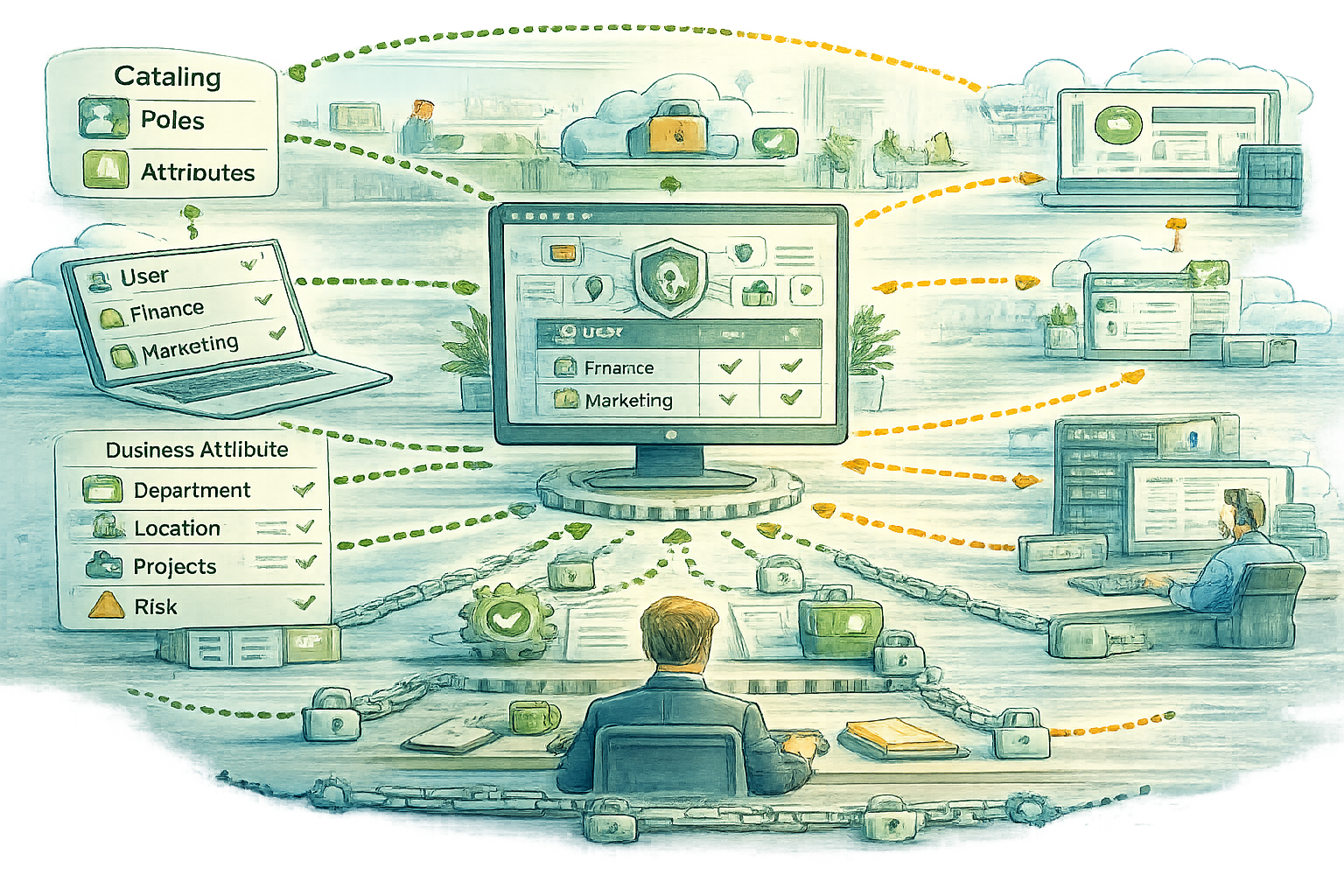
Role and entitlement governance is the layer that makes access understandable and controllable at scale. Instead of granting permissions one-by-one, access is structured into business roles and entitlement bundles that map to how your organization works, while still supporting fine-grained policies using attributes (department, location, customer tier, risk signals, etc.). This creates a clear catalog of “who can get what” and the logic behind it, across both simple and complex applications.
Benefits: More consistent access decisions, cleaner least-privilege, and far less access sprawl over time. It speeds up onboarding and changes because access can be assigned through roles and policies, reduces the chance of over-provisioning, and gives compliance teams a much clearer line of sight into why access exists and whether it still makes sense.
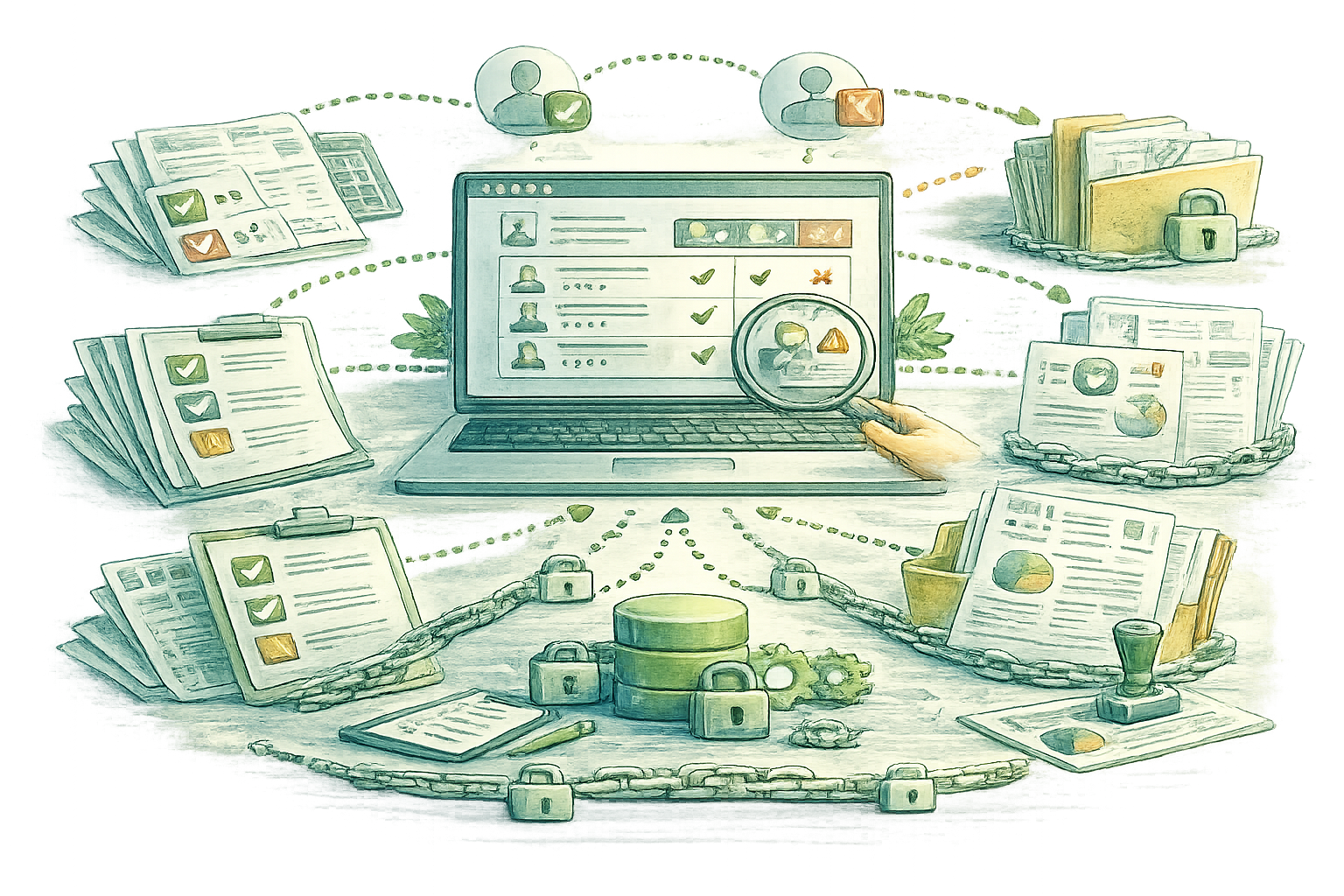
Access reviews are where IGA turns “who should have access” into a living, repeatable control. Instead of chasing spreadsheets, certifications bring managers, application owners, and control functions into a structured review cycle to confirm, adjust, or revoke access based on real business need and risk.
The result is cleaner entitlements and fewer standing privileges over time, with clear accountability on every decision. You also get audit-ready evidence and traceability for regulations and internal controls, and you can target high-risk systems more frequently while keeping low-risk reviews lightweight.
SoD turns policy into prevention. It detects risky combinations (for example, “create vendor” plus “approve payment”) and enforces rules during access requests, role assignments, and provisioning so conflicts are caught early, not discovered later during an audit or incident.
This reduces fraud and error exposure, and it standardizes how risk is assessed across applications and roles. It also accelerates approvals because reviewers see clear conflict context and remediation options (alternative roles, compensating controls, or exception workflows), while maintaining strong governance alignment with regulated environments.

Great IGA starts with a clean “source of truth”. This capability defines which systems are authoritative for which attributes (for example HR for employment status, directory for technical identifiers), then continuously reconciles and validates identity data across all connected systems. It catches duplicates, missing attributes, inconsistent department or manager data, and broken correlations before they ripple into wrong access decisions.
The benefit is reliability at scale. Cleaner identity data means fewer provisioning mistakes, fewer manual exceptions, and far less over-provisioning caused by bad or outdated attributes. It also improves joiner and mover automation, because policies and roles can be assigned with confidence, and it gives you a stable foundation for audits and regulatory evidence.
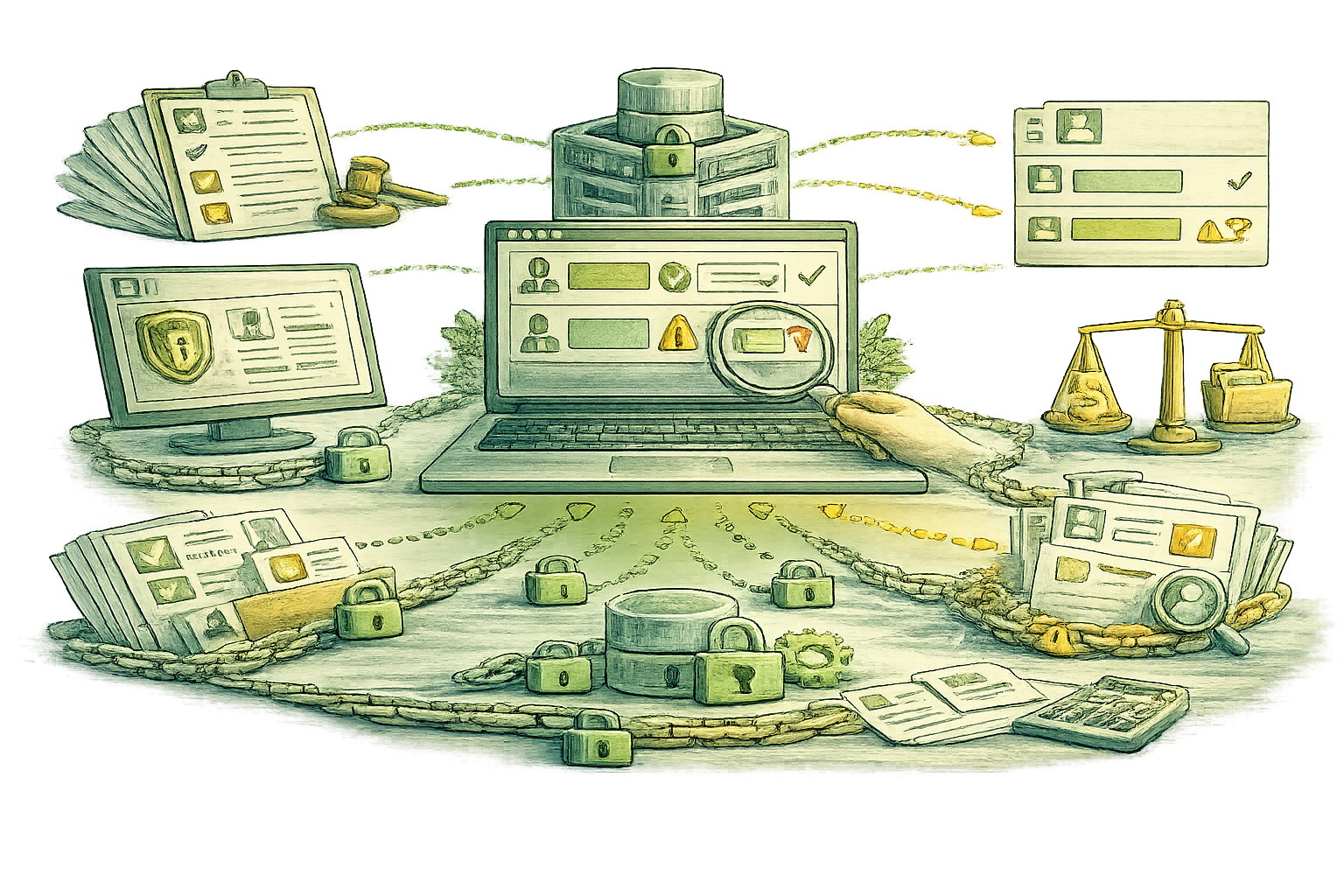
This capability turns identity governance into “always-audit-ready”. It captures end-to-end evidence for who has access to what, why they have it, who approved it, when it changed, and whether it violates policies or SoD controls. Instead of hunting through tickets and emails, you can produce structured reports and traceable audit trails across lifecycle events, requests, approvals, provisioning, and periodic reviews, including regulatory expectations like strong access governance and audit trails.
The benefit is faster audits with fewer findings. You reduce audit preparation from weeks to hours by generating consistent, repeatable evidence packs for frameworks and regulations like ISO 27001, SOC 2, SOX, GDPR, and NIS2, plus finance regulators where applicable (for example BaFin and ACPR). It also supports continuous compliance, because gaps (stale access, missing approvals, unreviewed entitlements) become visible early, not at audit time.
How We Deliver Successful IGA Programs
We deliver IGA as a program, not a one-time implementation. Our approach combines governance, scalable onboarding, and reusable delivery methods to ensure adoption and measurable outcomes.







