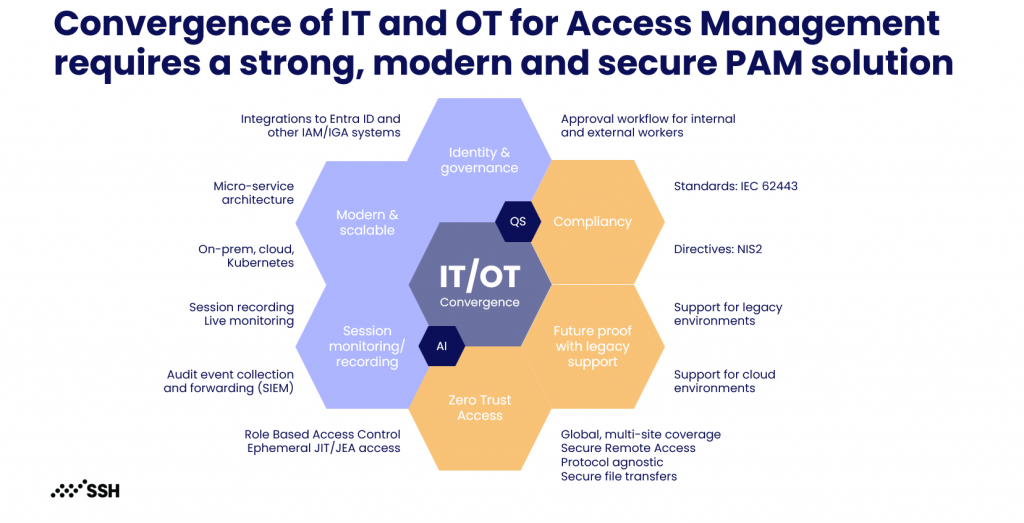
SSH PrivX is a Privileged Access Management (PAM) solution built for modern, Zero Trust privileged access. It helps organizations control and monitor privileged access to servers, cloud resources, and sensitive systems through identity-based, just-in-time access with strong authentication, traceability, and reduced reliance on shared passwords.
PrivX is also well suited for environments where cryptographic resilience and system constraints matter. For organizations preparing for post-quantum risk and for OT environments where traditional PAM agents and workflows are hard to operate, PrivX supports controlled access approaches that can be adapted to critical infrastructure and industrial systems.
What you can achieve with SSH PrivX
- Enable just-in-time privileged access with time-bound approvals
- Reduce or eliminate shared admin passwords with identity-based access
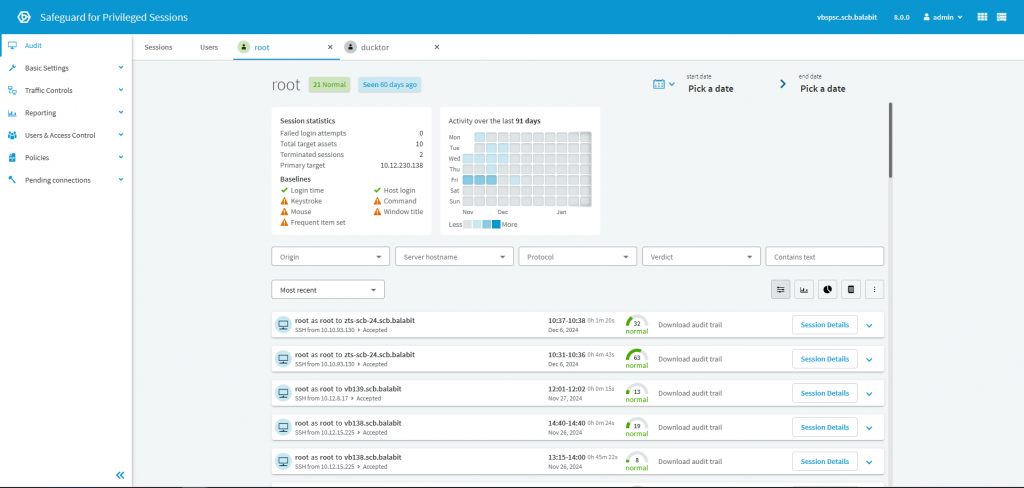
- Improve audit readiness with traceability, session visibility, and reporting
- Support PAM for OT use cases with controlled access to critical systems and constrained environments
- Strengthen long-term security posture by aligning privileged access with crypto-resilience goals, including post-quantum readiness planning
How Security Accent delivers SSH PrivX successfully
We implement PrivX as part of a practical PAM program for IT and, when required, OT. We support you from scope definition and access policy design to phased onboarding, operational readiness, and continuous optimization, ensuring adoption and sustainable governance.
Our typical delivery includes
- PAM scope definition (IT/OT), user groups, and privileged access flows
- Target architecture and access policies (approvals, time-bound access, least privilege)
- PrivX implementation, configuration, and integration with your identity provider
- Onboarding of priority systems (servers, critical platforms, OT jump access patterns), then phased expansion
- Operational procedures, admin enablement, and post go-live stabilization
Need help with SSH PrivX?
Share your scope (IT and/or OT), priority systems, and access workflows. We will respond with recommended next steps. If you prefer to talk first, book a short discovery call.