Gluu Flex is an enterprise identity and access management software distribution for organizations that need to self-host authentication and authorization services. It is built to run as a highly available, performant, multi-datacenter IAM platform when data sovereignty, security requirements, or scale make SaaS limiting. Flex is Gluu’s flagship product: a commercial Identity Provider with an open source core, combining the Linux Foundation Janssen components with the Flex Admin UI and an enterprise control plane that adds features like reporting and audit.
What you can achieve with Gluu Flex
- Workforce and CIAM federation with SAML and OpenID Connect, plus SSO
- MFA and passwordless authentication, including step-up authentication for sensitive access
- Identity orchestration for flexible web and mobile authentication journeys
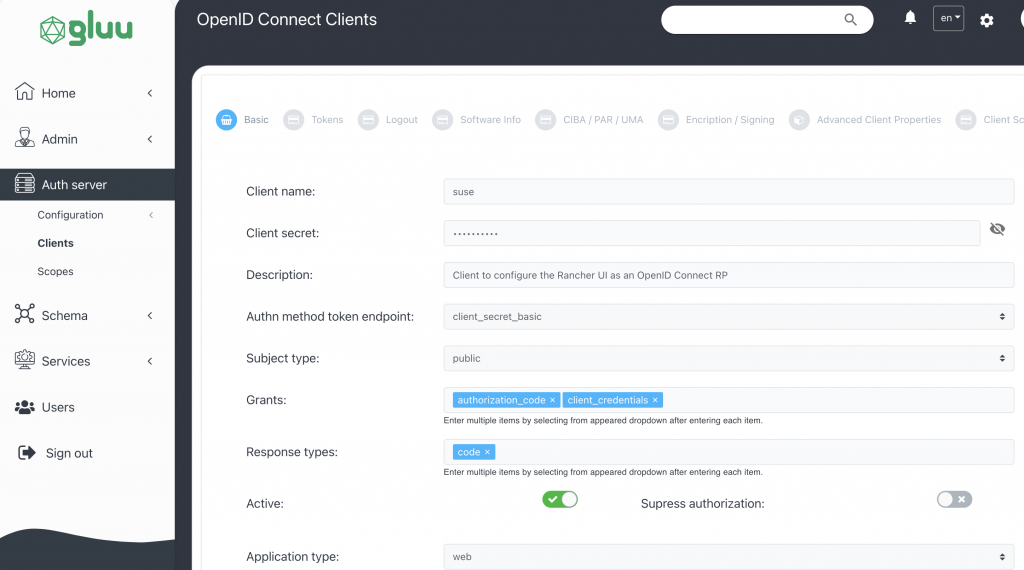
- API client management and dynamic registration to support modern app and API ecosystems
- Support advanced scenarios such as Open Banking and OAuth federation through software statement key material publication
How Security Accent delivers Gluu Flex successfully
We deliver Gluu Flex as a structured access program, not only a platform setup. We help you design the target architecture and authentication journeys, implement federation and policies, and prepare operations for high availability and audit-ready governance in self-hosted environments.
Our typical delivery includes
- Target architecture and rollout planning for self-hosted IAM infrastructure (HA and multi-environment readiness)
- Federation configuration (OIDC/SAML), token/session design, and policy baseline
- MFA, passwordless, and step-up authentication implementation aligned to your use cases
- API client management and integration approach for applications and APIs
- Operational readiness: reporting/audit enablement, logging, monitoring, runbooks, and knowledge transfer
Need help with Gluu Flex?
Share your scope, target applications, and hosting approach. We will respond with recommended next steps. If you prefer to talk first, book a short discovery call.