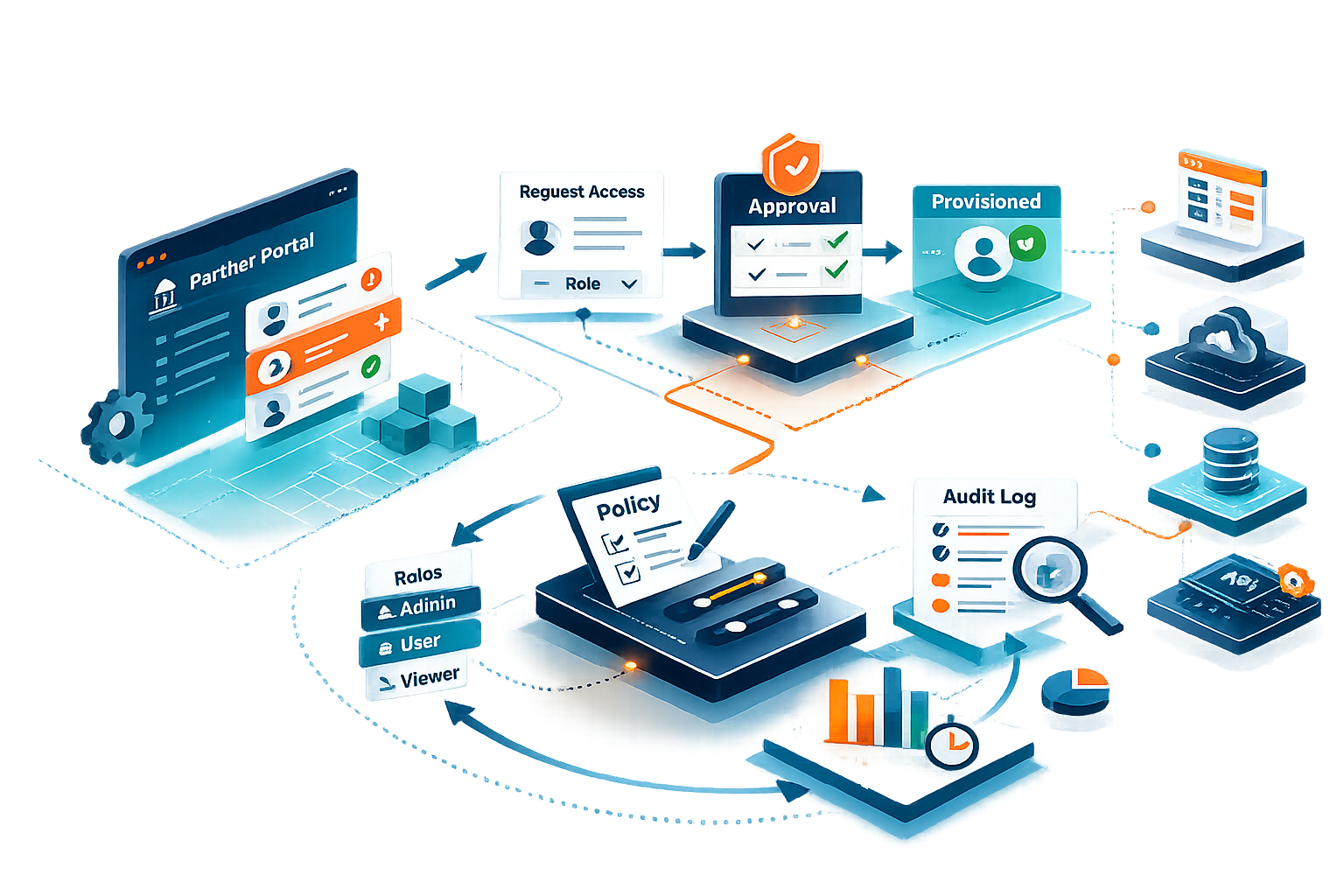
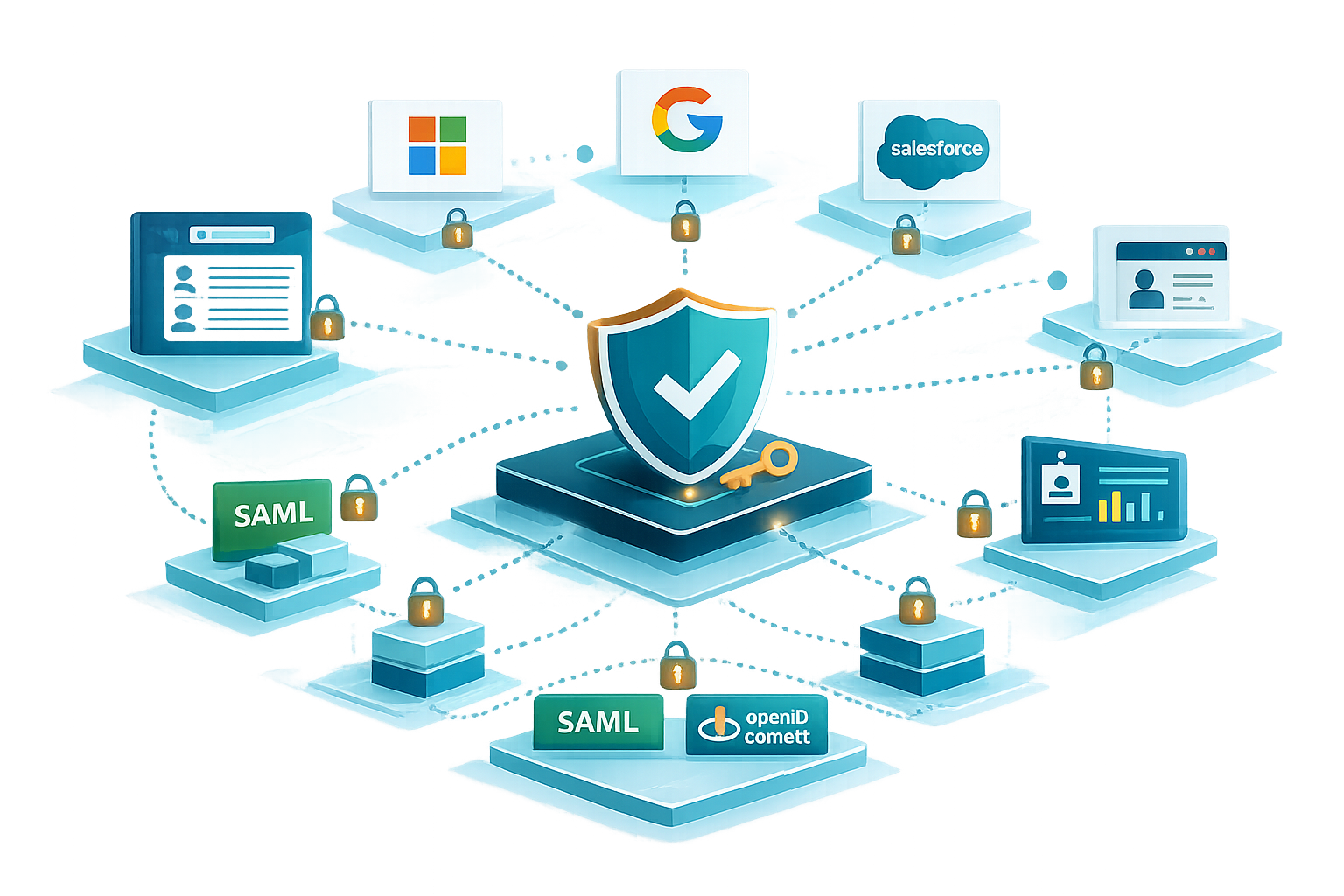
We help you implement a practical onboarding and governance model for external users so partner access stays controlled, up to date, and auditable. We design registration or invitation flows, approvals and ownership, role and entitlement mapping, and lifecycle controls aligned to contracts and projects. Where needed, we enable delegated administration so partners can manage their own employees within an approved scope, without losing central control or auditability.
Typical deliverables:
Partner onboarding flow design (invitation, registration, verification, terms and consent where needed)
Access request and approval model (who approves what, internal owners, exception handling)
Delegated administration model for partners (partner admins, scoping rules, what can be managed, guardrails)
Partner role and entitlement model (mapping to applications, data sets, and APIs)
Lifecycle governance controls (change triggers, suspension, offboarding, recertification cadence)
Reporting and audit evidence model (traceability, delegated actions logging, access reviews, ownership)