OT IAM succeeds when it integrates with your existing identity sources and becomes part of daily operations. We implement the selected controls, integrate directories and identity sources, onboard OT systems in iterations, and establish the processes and runbooks needed for sustainable operations. The output is a working capability that scales across plants and vendors with consistent control and traceability.
Typical deliverables:
Integration with identity sources and admin model (AD/Entra ID, LDAP, MFA, group/role mapping)
Onboarding approach for OT systems and zones (by site, by asset class, by criticality)
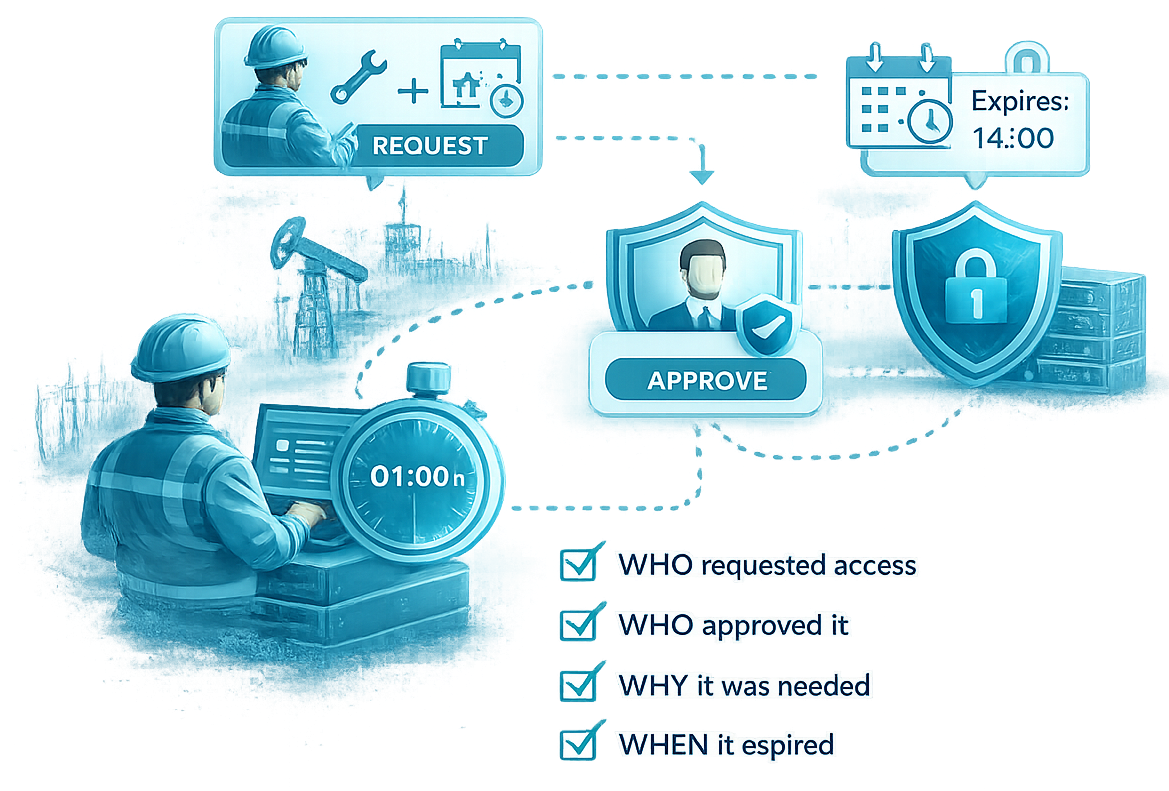
Access session accountability setup (logging, monitoring/recording where required, traceability to identity)
Operational runbooks (onboarding/offboarding, access requests, incident response support, reviews)
Production readiness and handover (training, KPIs, support model, governance cadence)