Third-Party and Vendor Privileged Access
Third-Party and Vendor Privileged Access: secure external access without shared credentials
Vendors and third parties often need privileged access to support critical systems, but traditional approaches create risk: shared passwords, unmanaged VPN access, and limited visibility into what was actually done. That weak accountability increases breach impact and makes audits and investigations harder.
Modern privileged access enables external users to connect securely with strong authentication, time-bound access where needed, and full traceability of privileged activity. We help you onboard vendors safely, keep access within clear boundaries, and make every session accountable and auditable.
Need to enable vendor access while keeping full control and traceability?
If you already know your scope and priority vendors, send an inquiry and we will respond with recommended next steps Tell us about your needs.
Third-Party and Vendor Privileged Access
What Third-Party Privileged Access Delivers
- Vendor Access Discovery and Risk Baseline
- Strong Authentication and Access Boundaries
- Time-Bound Vendor Access and Approvals
- Privileged Session Oversight and Evidence
- Credential Sharing Elimination and Secrets Control
- Vendor Lifecycle Governance and Access Reviews
- Privileged Access Compliance and Audit Evidence
- Operational Model and Continuous Optimization
Third-party access is often spread across VPN accounts, shared admin credentials, jump hosts, and local privileged users that are hard to track. This capability builds a clear view of which vendors access which systems, how access is granted today, and where the highest-risk paths and weakest accountability exist.
This makes risk visible and actionable. It helps prioritize the vendors and systems that need immediate control, reduces unknown exposure, and creates a defensible baseline to measure improvements in governance and audit readiness.

Vendor access becomes risky when authentication is weak or access is broader than required. This capability enforces strong authentication, applies clear boundaries to what vendors can reach, and uses policy controls to align access with business need and risk.
This reduces the chance of compromise and lateral movement, while keeping vendor support practical. It improves confidence that external access is limited to the right systems, at the right times, under the right conditions.

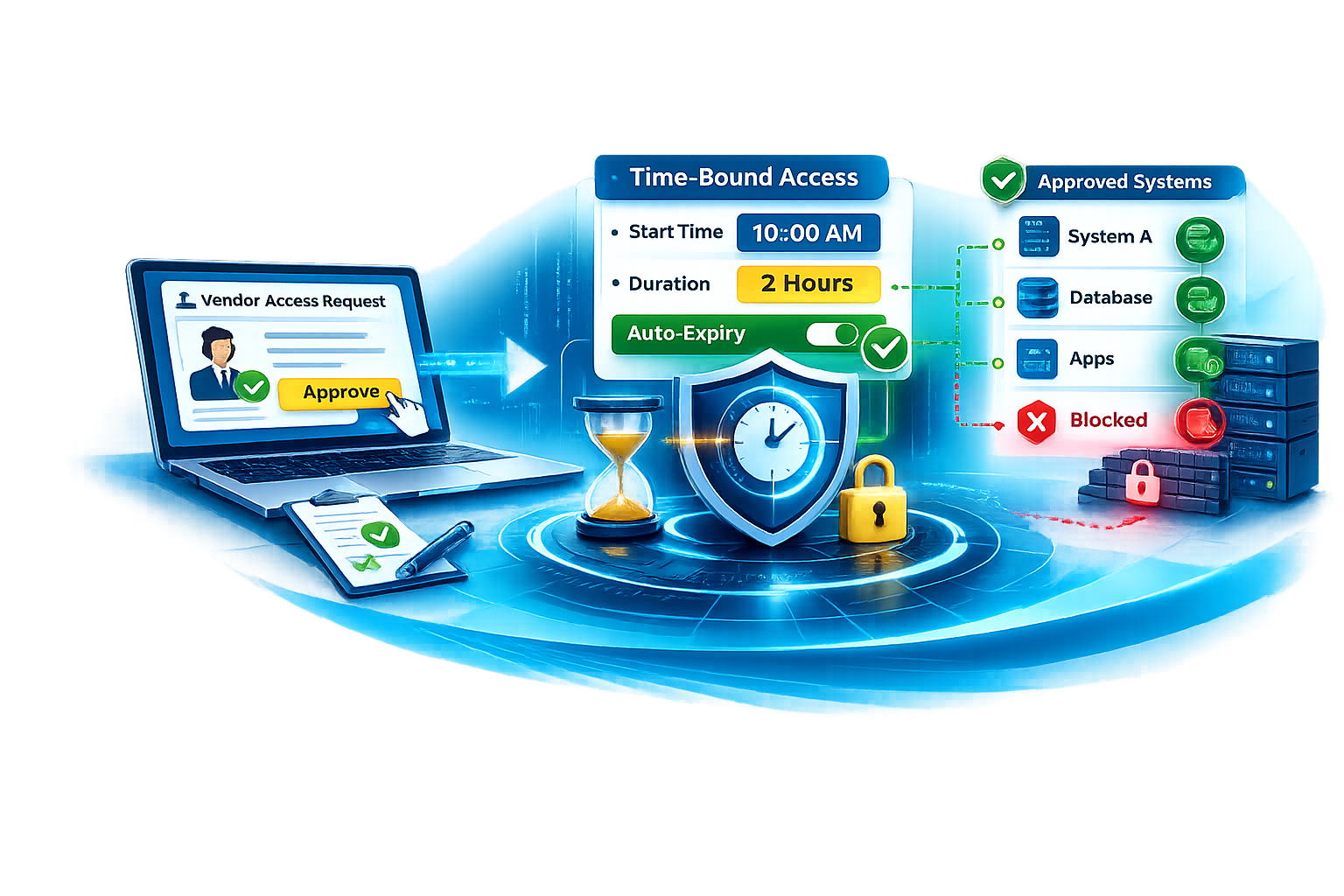
Third-party privileged access is safest when it is granted only when needed and expires automatically. This capability introduces controlled access windows for vendors, with clear approval rules tied to system criticality, support cases, and risk context, so vendor access does not remain open beyond the intended purpose.
This keeps vendor support practical while reducing standing access and limiting “always-on” exposure. It also improves accountability because every access window is traceable to a request, an approval decision, a time limit, and a defined scope.
When vendors connect to critical systems, knowing that access happened is not enough. This capability provides visibility into privileged sessions, including session oversight and, where required, recording and evidence capture, so actions taken during vendor access can be reviewed and investigated reliably.
This strengthens incident response and audit readiness by making vendor activity provable and defensible. It also deters misuse, accelerates investigations, and builds confidence that third-party access remains within approved boundaries.

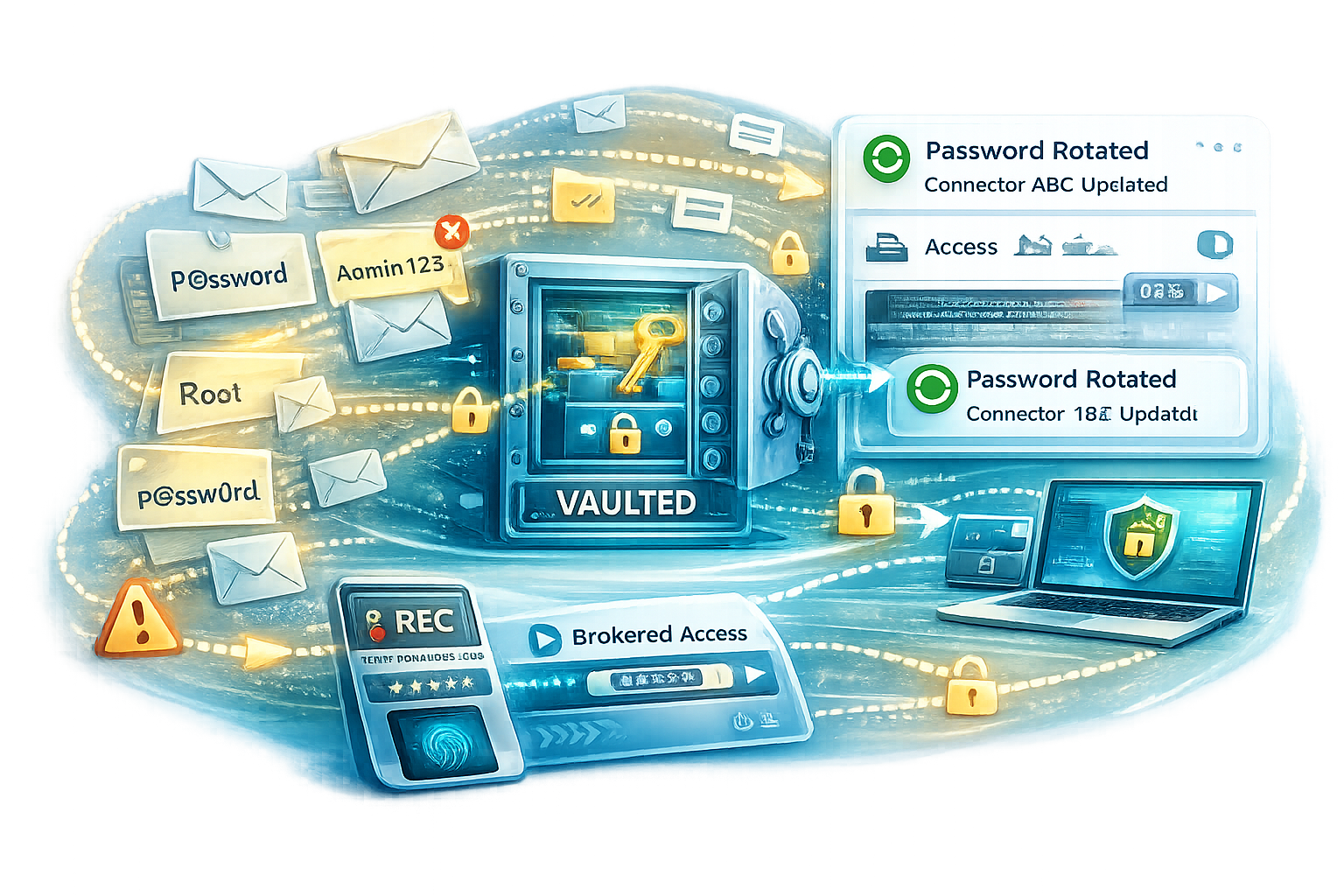
Vendor access often becomes risky because passwords and admin credentials get shared across tickets, emails, and teams, then remain valid long after the work is done. This capability removes that practice by introducing controlled credential handling, including vaulting and rotation where needed, and brokered access methods that avoid exposing privileged secrets to vendors.
The result is a major reduction in credential leakage risk and “unknown reuse.” It also limits the blast radius of compromise, supports cleaner operations during incidents, and improves confidence that vendors cannot keep using privileged credentials outside approved work windows.
Third-party access changes constantly with contracts, projects, and support relationships. This capability keeps vendor access accurate over time through lifecycle controls such as onboarding rules, suspension and offboarding, periodic access reviews, and clear ownership for who validates vendor access to specific systems.
This prevents access drift, reduces orphaned vendor accounts, and improves audit readiness because access remains explainable and provable. It also reduces operational friction by making vendor access maintenance predictable rather than reactive.

Third-party access is often where auditors ask the hardest questions because it crosses organizational boundaries. This capability brings vendor access evidence into one place across requests, approvals, time windows, credential use, and session activity, so privileged vendor work becomes traceable and provable against audit and regulatory expectations.
The outcome is faster audits and fewer findings because evidence is complete and consistent. It also strengthens investigations by making it easy to explain who accessed what, when, why it was approved, and what actions were performed.

Vendor access changes with contracts, projects, and support needs, and controls drift when ownership is unclear. This capability defines how third-party privileged access is run day to day including ownership, onboarding and offboarding workflows, access change handling, monitoring, and escalation so access remains controlled as vendors and systems evolve.
This reduces operational friction and prevents “shadow” access paths from reappearing over time. It keeps third-party access sustainable at scale, with policies that remain consistent, visible, and enforceable long after go-live.

How We Deliver Successful Vendor Privileged Access Projects
Successful vendor access is fast for third parties and controlled for you. We focus on enabling support without credential sharing, keeping access within clear boundaries, and ensuring every session is traceable and defensible.